With the Swiss Federal Council’s decision to bring the Information Security Act (ISG) and the corresponding ordinance into force on January 1, 2024, Switzerland is sending a clear signal for increased information security and cyber security. In this context, Swiss GRC organized a webinar that gave participants an insight into the upcoming legal changes as well as practical implementation options through a live demonstration of the GRC Toolbox.
The imminent entry into force at the beginning of the new year of the Information Security Act (ISG) and the Information Security Ordinance (ISV) marks a turning point in information security that will occupy numerous organizations intensively in the coming months and years. With this in mind, the webinar launched by Swiss GRC aimed to provide crucial information and insights on how to effectively meet the key requirements of the ISG and ISV. Besfort Kuqi, CEO and co-founder of Swiss GRC, opened the webinar and got the participants in the mood for the program.
Insight into the significance and scope of the Information Security Act (ISG)
Reto Zbinden, Lawyer and CEO of Swiss Infosec AG, gave an introduction to the Information Security Act (ISG). He discussed the key aspects of the law, explained what it means to be ISG-compliant and summarized the objectives of the ISG. In doing so, he addressed the key requirements, processes and evidence needed for effective implementation. Finally, he made it clear that the increasing pressure to implement security measures is driving organizations to move away from traditional methods such as Excel or Word and instead use specialized tools to meet the complex requirements.
A GRC(O) framework for successful ISG/ISV implementation
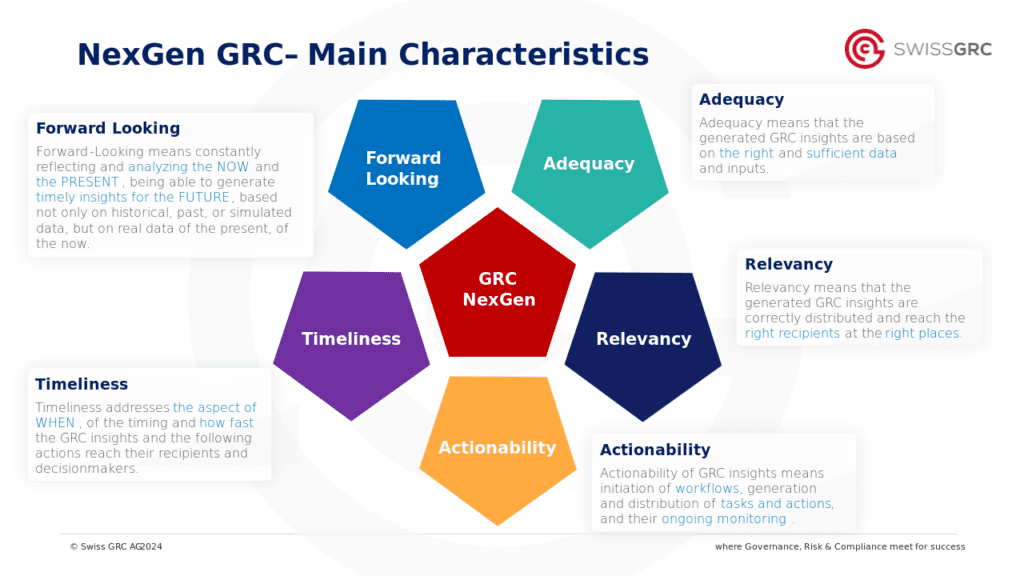
In the second part of the webinar, Besfort Kuqi used a product demo to show how the Information Security Act (ISG) and the Information Security Regulation (ISV) can be implemented with the help of software such as the GRC Toolbox. As a proven ISMS industry solution, it supports organizations in implementing the ISG/ISV requirements. Besfort Kuqi not only spoke about the classic GRC approach, but went one step further and presented a GRC(O) framework to highlight the support of the GRC Toolbox for information security operations in accordance with Art. 25 (review of protection requirements and circle of authorized persons), Art. 27 (security procedures), Art. 28 (assignment to the security levels “high protection” and “very high protection”) and Art. 29 (security measures) of the ISG.

GRC(O) Framework © Swiss GRC AG 2023
As the graphic above makes clear, the software offers comprehensive support in the area of governance, in particular in setting up an information security management system (ISMS) in accordance with Art. 5 of the ISG. In the area of risk management, the functionality of the software includes important aspects such as the inventory of protected objects (Art. 7), coordination with third parties (Art. 10) and incident management (Art. 12). In the area of compliance, the software provides valuable support in the maintenance of legal bases and contractual obligations (Art. 6), in training and awareness-raising measures (Art. 11) and in the planning and implementation of controls and audits (Art. 13).
Watch the webinar recording now (in German)





 DE
DE